Add description, images, menus and links to your mega menu
A column with no settings can be used as a spacer
Link to your collections, sales and even external links
Add up to five columns
Add description, images, menus and links to your mega menu
A column with no settings can be used as a spacer
Link to your collections, sales and even external links
Add up to five columns
- Overview
- Specifications
- Enterprise and Government
- Local Service & Support
The YubiHSM 2 is a game changing hardware solution for protecting Certificate Authority root keys from being copied by attackers, malware, and malicious insiders. It offers superior cost effective security and easy deployment making it accessible for every organization. It offers a higher level of security for cryptographic digital key generation, storage, and management, for organizations running Microsoft Active Directory Certificate Services.
The YubiHSM 2 features are accessible by integrating with an open source and comprehensive software development toolkit (SDK) for a wide range of open source and commercial applications. The most common use case is hardware-based digital signature generation and verification. In additional emerging use cases such as securing cryptocurrency exchanges and IoT gateways are just a few examples of how the world’s smallest HSM can secure modern infrastructures.
YubiHSM 2 secures cryptographic keys through their entire lifecycle from secure key generation, attestation, secure key storage, secure key distribution, secure key backup all the way to secure key destruction if needed. Screen reader support enabled.
Product Features (Business)
- Direct USB Support
- General Purpose HSM
- Introduces asymmetric cryptography
- Windows, Linux, and Mac support
- USB-A, IP68 rated, Crush Resistant, No Batteries Required, No Moving Parts
Secure key storage and operations
Create, import, and store keys, then perform all crypto operations in the HSM hardware to prevent theft of keys while at rest or in use. This protects against both logical attacks against the server, such as zero-day exploits or malware, and physical theft of a server or its hard drive.
Extensive cryptographic capabilities
YubiHSM 2 supports hashing, key wrapping, asymmetric signing and decryption operations including advanced signing using ed25519. Attestation is also supported for asymmetric key pairs generated on-device.
Secure session between HSM and application
The integrity and privacy of commands and data in transit between the HSM and applications are protected using a mutually authenticated, integrity and confidentiality protected tunnel.
Role-based access controls for key management and key usage
All cryptographic keys and other objects in the HSM belong to one or more security domains. Access rights are assigned for each authentication key at creation time which allow a specific set of cryptographic or management operations to be performed per security domain. Admins assign rights to authentication keys based on its use case, such as a event monitoring app that needs the ability to read all audit logs in the HSM, or a Registration Authority that needs to issue (sign) end user digital certificates, or a domain security admin who needs to create and delete crypto keys.
16 concurrent connections
Multiple applications can establish sessions with a YubiHSM to perform cryptographic operations. Sessions can be automatically terminated after inactivity or be long-lived to improve performance by eliminating session creation time.
Network Shareable
To increase the flexibility of deployments, the YubiHSM 2 can be made available for use over the network by applications on other servers. This can be especially advantageous on a physical server that is hosting multiple virtual machines.
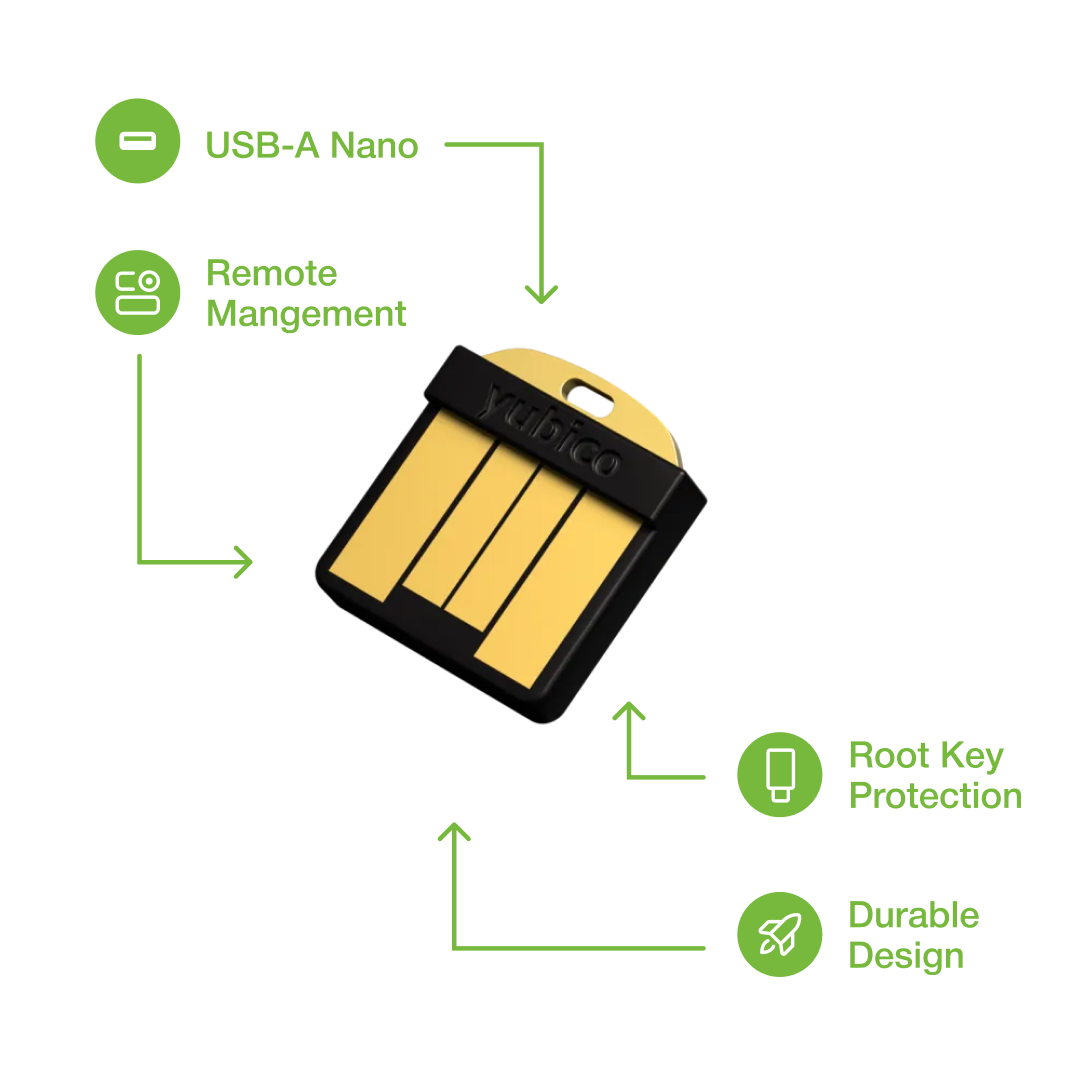
Remote Management
Easily manage multiple deployed YubiHSMs remotely for the entire enterprise – eliminate on-call staff complexity and travel expense.
Unique “Nano” form factor, low-power usage
The Yubico “Nano” form factor allows the HSM to be inserted completely inside a USB-A port so it’s completely concealed – no external parts that protrude out of the server back or front chassis. It uses minimal power, max of 30mA, for cost-savings on your power budget.
M of N wrap key Backup and Restore
Backing up and deploying cryptographic keys on multiple HSMs is a critical component of an enterprise security architecture, but it’s a risk to allow a single individual to have that ability. The YubiHSM supports setting M of N rules on the wrap key used to export keys for backup or transport, so that multiple administrators are required to import and decrypt a key to make it usable on additional HSMs. For example in an enterprise, the Active Directory root CA private key might be key wrapped for 7 administrators (N=7) and at least 4 of them (M=4) are required to import and unwrap (decrypt) the key in the new HSM.
Interfaces via YubiHSM KSP, PKCS#11, and native libraries
Crypto enabled applications can leverage the YubiHSM via Yubico’s Key Storage Provider (KSP) for Microsoft’s CNG or industry-standard PKCS#11. Native libraries are also available on Windows, Linux and macOS to enable more direct interaction with the device’s capabilities.
Tamper evident Audit Logging
The YubiHSM internally stores a log of all management and crypto operation events that occur in the device and that log can be exported for monitoring and reporting. Each event (row) in the log is hash chained with the previous row and signed so that it’s possible to determine if any events are modified or deleted.
Direct USB Support
The YubiHSM 2 can talk directly to the USB layer without the need for an intermediate HTTP mechanism. This delivers an improved experience for the developers who are developing solutions for virtualised environments.
YubiKeys are made in USA and Sweden (EU). Trust Panda ships globally (except to sanctioned or embargoed countries).
| UPC/GTIN | 5060408464571 |
| USB Type | USB-A |
| NFC-enabled | No |
| Firmware | 2.2 |
| Linux | CentOS 7 Debian 8 Debian 9 Debian 10 Fedora 28 Fedora 30 Fedora 31 Ubuntu 1404 Ubuntu 1604 Ubuntu 1804 Ubuntu 1810 Ubuntu 1904 Ubuntu 1910 |
| Windows | Windows 10 Windows Server 2012 Windows Server 2016 Windows Server 2019 |
| macOS | 10.12 Sierra 10.13 High Sierra 10.14 Mojave |
| Cryptographic interfaces (APIs) | Microsoft CNG (KSP) PKCS#11 (Windows, Linux, macOS) Native YubiHSM Core Libraries (C, python) |
| Cryptographic capabilities |
Hashing (used with HMAC and asymmetric signatures) RSA Elliptic Curve Cryptography (ECC) Key wrap Random numbers Attestation |
| Performance | Performance varies depending on usage. The accompanying Software Development Kit includes performance tools that can be used for additional measurements. Example metrics from an otherwise unoccupied YubiHSM 2 RSA-2048-PKCS1-SHA256: ~139ms avg RSA-3072-PKCS1-SHA384: ~504ms avg RSA-4096-PKCS1-SHA512: ~852ms avg ECDSA-P256-SHA256: ~73ms avg ECDSA-P384-SHA384: ~120ms avg ECDSA-P521-SHA512: ~210ms avg EdDSA-25519-32Bytes: ~105ms avg EdDSA-25519-64Bytes: ~121ms avg EdDSA-25519-128Bytes: ~137ms avg EdDSA-25519-256Bytes: ~168ms avg EdDSA-25519-512Bytes: ~229ms avg EdDSA-25519-1024Bytes: ~353ms avg AES-(128|192|256)-CCM-Wrap: ~10ms avg HMAC-SHA-(1|256): ~4ms avg HMAC-SHA-(384|512): ~243ms avg |
| Storage Capacity |
All data stored as objects. 256 object slots, 128KB (base 10) max total Stores up to 127 rsa2048, 93 rsa3072, 68 rsa4096 or 255 of any elliptic curve type, assuming only one authentication key is present Object types: Authentication keys (used to establish sessions); asymmetric private keys; opaque binary data objects, e.g. x509 certs; wrap keys; HMAC keys |
| Management | Mutual authentication and secure channel between applications and HSM M of N unwrap key restore via YubiHSM Setup Tool |
| Software Development Kit | YubiHSM Core Library (libyubihsm) for C, Python YubiHSM Shell (Configuration CLI) PKCS#11 Module YubiKey Key Storage Provider (KSP) for use with Microsoft YubiHSM Connector YubiHSM Setup Tool Documentation and code examples |
| Physical Characteristics | Form factor: ‘nano’ designed for confined spaces such as internal USB ports in servers Dimensions: 12mm x 13mm x 3.1mm Weight: 1 gram Current requirements 20mA avg, 30mA max USB-A plug connector |
| Safety and environmental compliance | FCC CE WEEE ROHS |
| Host Interface | Universal Serial Bus (USB) 1.x Full Speed (12Mbit/s) Peripheral with bulk interface. |
Trust Panda has a dedicated Enterprise and Government team. Please don't hesitate to contact us for the following:
Large deployments
Planning to deploy more than 200 YubiKeys in a 12 month period? Our sales team can prepare a custom price quote. Give us a call, message us or complete the contact form below and we'll get this over to you for review.
FIPS Keys
Depending on your requirement, your organisation may require a FIPS certified key.
Direct Employee Delivery
If you're a business that needs to ship YubiKeys to employees locally or globally, we can take away the pain of shipping your keys to your team. Just 7 easy steps and your team will be up and running with YubiKey. We'd be happy to help customise a dispatch and delivery model to streamline your deployment process.
Enterprise Self Service Portal
Trust Panda can offer a dedicated ordering portal that is integrated with your organisations single sign on system, with role based access.
YubiEnterprise Subscription
Flexible licensing approach to obtain industry-leading and trusted YubiKey hardware authentication, providing great flexibility and complete peace of mind.
Purchase Order/P-Card/Corporate Charge Card
Trust Panda offers flexible payment options to approved customers.
When you buy your YubiKey at Trust Panda, you're not just buying from Australia's number one Gold Certified Yubico Reseller.
With business hours phone, live chat and a Sydney based customer support team we have an incredible depth of knowledge and experience working with the Yubico product range.
At Trust Panda your product comes with a manufacturers warranty in addition to your rights under the Australian Consumer Law our our customer support team manage this in house so no need to get in touch with the manufacturer.
Product Compatibility
YubiHSM is a hardware security module. This product is special order and requires validation before it can be ordered.
Product Setup
Ready to get started? Click here.
Questions?
Have a question? Please don't hesitate to contact us.
Recently viewed products
- Overview
- Specifications
- Enterprise and Government
- Local Service & Support
The YubiHSM 2 is a game changing hardware solution for protecting Certificate Authority root keys from being copied by attackers, malware, and malicious insiders. It offers superior cost effective security and easy deployment making it accessible for every organization. It offers a higher level of security for cryptographic digital key generation, storage, and management, for organizations running Microsoft Active Directory Certificate Services.
The YubiHSM 2 features are accessible by integrating with an open source and comprehensive software development toolkit (SDK) for a wide range of open source and commercial applications. The most common use case is hardware-based digital signature generation and verification. In additional emerging use cases such as securing cryptocurrency exchanges and IoT gateways are just a few examples of how the world’s smallest HSM can secure modern infrastructures.
YubiHSM 2 secures cryptographic keys through their entire lifecycle from secure key generation, attestation, secure key storage, secure key distribution, secure key backup all the way to secure key destruction if needed. Screen reader support enabled.
Product Features (Business)
- Direct USB Support
- General Purpose HSM
- Introduces asymmetric cryptography
- Windows, Linux, and Mac support
- USB-A, IP68 rated, Crush Resistant, No Batteries Required, No Moving Parts
Secure key storage and operations
Create, import, and store keys, then perform all crypto operations in the HSM hardware to prevent theft of keys while at rest or in use. This protects against both logical attacks against the server, such as zero-day exploits or malware, and physical theft of a server or its hard drive.
Extensive cryptographic capabilities
YubiHSM 2 supports hashing, key wrapping, asymmetric signing and decryption operations including advanced signing using ed25519. Attestation is also supported for asymmetric key pairs generated on-device.
Secure session between HSM and application
The integrity and privacy of commands and data in transit between the HSM and applications are protected using a mutually authenticated, integrity and confidentiality protected tunnel.
Role-based access controls for key management and key usage
All cryptographic keys and other objects in the HSM belong to one or more security domains. Access rights are assigned for each authentication key at creation time which allow a specific set of cryptographic or management operations to be performed per security domain. Admins assign rights to authentication keys based on its use case, such as a event monitoring app that needs the ability to read all audit logs in the HSM, or a Registration Authority that needs to issue (sign) end user digital certificates, or a domain security admin who needs to create and delete crypto keys.
16 concurrent connections
Multiple applications can establish sessions with a YubiHSM to perform cryptographic operations. Sessions can be automatically terminated after inactivity or be long-lived to improve performance by eliminating session creation time.
Network Shareable
To increase the flexibility of deployments, the YubiHSM 2 can be made available for use over the network by applications on other servers. This can be especially advantageous on a physical server that is hosting multiple virtual machines.
Remote Management
Easily manage multiple deployed YubiHSMs remotely for the entire enterprise – eliminate on-call staff complexity and travel expense.
Unique “Nano” form factor, low-power usage
The Yubico “Nano” form factor allows the HSM to be inserted completely inside a USB-A port so it’s completely concealed – no external parts that protrude out of the server back or front chassis. It uses minimal power, max of 30mA, for cost-savings on your power budget.
M of N wrap key Backup and Restore
Backing up and deploying cryptographic keys on multiple HSMs is a critical component of an enterprise security architecture, but it’s a risk to allow a single individual to have that ability. The YubiHSM supports setting M of N rules on the wrap key used to export keys for backup or transport, so that multiple administrators are required to import and decrypt a key to make it usable on additional HSMs. For example in an enterprise, the Active Directory root CA private key might be key wrapped for 7 administrators (N=7) and at least 4 of them (M=4) are required to import and unwrap (decrypt) the key in the new HSM.
Interfaces via YubiHSM KSP, PKCS#11, and native libraries
Crypto enabled applications can leverage the YubiHSM via Yubico’s Key Storage Provider (KSP) for Microsoft’s CNG or industry-standard PKCS#11. Native libraries are also available on Windows, Linux and macOS to enable more direct interaction with the device’s capabilities.
Tamper evident Audit Logging
The YubiHSM internally stores a log of all management and crypto operation events that occur in the device and that log can be exported for monitoring and reporting. Each event (row) in the log is hash chained with the previous row and signed so that it’s possible to determine if any events are modified or deleted.
Direct USB Support
The YubiHSM 2 can talk directly to the USB layer without the need for an intermediate HTTP mechanism. This delivers an improved experience for the developers who are developing solutions for virtualised environments.
YubiKeys are made in USA and Sweden (EU). Trust Panda ships globally (except to sanctioned or embargoed countries).
| UPC/GTIN | 5060408464571 |
| USB Type | USB-A |
| NFC-enabled | No |
| Firmware | 2.2 |
| Linux | CentOS 7 Debian 8 Debian 9 Debian 10 Fedora 28 Fedora 30 Fedora 31 Ubuntu 1404 Ubuntu 1604 Ubuntu 1804 Ubuntu 1810 Ubuntu 1904 Ubuntu 1910 |
| Windows | Windows 10 Windows Server 2012 Windows Server 2016 Windows Server 2019 |
| macOS | 10.12 Sierra 10.13 High Sierra 10.14 Mojave |
| Cryptographic interfaces (APIs) | Microsoft CNG (KSP) PKCS#11 (Windows, Linux, macOS) Native YubiHSM Core Libraries (C, python) |
| Cryptographic capabilities |
Hashing (used with HMAC and asymmetric signatures) RSA Elliptic Curve Cryptography (ECC) Key wrap Random numbers Attestation |
| Performance | Performance varies depending on usage. The accompanying Software Development Kit includes performance tools that can be used for additional measurements. Example metrics from an otherwise unoccupied YubiHSM 2 RSA-2048-PKCS1-SHA256: ~139ms avg RSA-3072-PKCS1-SHA384: ~504ms avg RSA-4096-PKCS1-SHA512: ~852ms avg ECDSA-P256-SHA256: ~73ms avg ECDSA-P384-SHA384: ~120ms avg ECDSA-P521-SHA512: ~210ms avg EdDSA-25519-32Bytes: ~105ms avg EdDSA-25519-64Bytes: ~121ms avg EdDSA-25519-128Bytes: ~137ms avg EdDSA-25519-256Bytes: ~168ms avg EdDSA-25519-512Bytes: ~229ms avg EdDSA-25519-1024Bytes: ~353ms avg AES-(128|192|256)-CCM-Wrap: ~10ms avg HMAC-SHA-(1|256): ~4ms avg HMAC-SHA-(384|512): ~243ms avg |
| Storage Capacity |
All data stored as objects. 256 object slots, 128KB (base 10) max total Stores up to 127 rsa2048, 93 rsa3072, 68 rsa4096 or 255 of any elliptic curve type, assuming only one authentication key is present Object types: Authentication keys (used to establish sessions); asymmetric private keys; opaque binary data objects, e.g. x509 certs; wrap keys; HMAC keys |
| Management | Mutual authentication and secure channel between applications and HSM M of N unwrap key restore via YubiHSM Setup Tool |
| Software Development Kit | YubiHSM Core Library (libyubihsm) for C, Python YubiHSM Shell (Configuration CLI) PKCS#11 Module YubiKey Key Storage Provider (KSP) for use with Microsoft YubiHSM Connector YubiHSM Setup Tool Documentation and code examples |
| Physical Characteristics | Form factor: ‘nano’ designed for confined spaces such as internal USB ports in servers Dimensions: 12mm x 13mm x 3.1mm Weight: 1 gram Current requirements 20mA avg, 30mA max USB-A plug connector |
| Safety and environmental compliance | FCC CE WEEE ROHS |
| Host Interface | Universal Serial Bus (USB) 1.x Full Speed (12Mbit/s) Peripheral with bulk interface. |
Trust Panda has a dedicated Enterprise and Government team. Please don't hesitate to contact us for the following:
Large deployments
Planning to deploy more than 200 YubiKeys in a 12 month period? Our sales team can prepare a custom price quote. Give us a call, message us or complete the contact form below and we'll get this over to you for review.
FIPS Keys
Depending on your requirement, your organisation may require a FIPS certified key.
Direct Employee Delivery
If you're a business that needs to ship YubiKeys to employees locally or globally, we can take away the pain of shipping your keys to your team. Just 7 easy steps and your team will be up and running with YubiKey. We'd be happy to help customise a dispatch and delivery model to streamline your deployment process.
Enterprise Self Service Portal
Trust Panda can offer a dedicated ordering portal that is integrated with your organisations single sign on system, with role based access.
YubiEnterprise Subscription
Flexible licensing approach to obtain industry-leading and trusted YubiKey hardware authentication, providing great flexibility and complete peace of mind.
Purchase Order/P-Card/Corporate Charge Card
Trust Panda offers flexible payment options to approved customers.
When you buy your YubiKey at Trust Panda, you're not just buying from Australia's number one Gold Certified Yubico Reseller.
With business hours phone, live chat and a Sydney based customer support team we have an incredible depth of knowledge and experience working with the Yubico product range.
At Trust Panda your product comes with a manufacturers warranty in addition to your rights under the Australian Consumer Law our our customer support team manage this in house so no need to get in touch with the manufacturer.
Product Compatibility
YubiHSM is a hardware security module. This product is special order and requires validation before it can be ordered.
Product Setup
Ready to get started? Click here.
Questions?
Have a question? Please don't hesitate to contact us.